Onion links offer/present/showcase a unique/intriguing/fascinating way to navigate the internet. These chains/links/trails of interconnected pages can lead/guide/transport you through a maze/labyrinth/network of information, often concealing/hiding/masking their true destination/purpose/goal until the very end. Unraveling onion links can be a thrilling/challenging/rewarding experience, requiring/demanding/insisting patience and a keen/sharp/observant eye for detail.
- Onion links/These linked networks/These concealed pathways often appear/seem/manifest as a series of simple pages/sites/URLs.
- Navigating/Unveiling/Deciphering these links can involve/demand/require clicking on hidden/subtle/unobvious text/links/buttons.
- Each/Every/Individual click may lead/bring/transport you to a new/different/fresh page, slowly revealing/unveiling/exposing the full picture/complexity/narrative.
Unmasking Hidden Networks: A Guide to Onion Links
The obscurity of the internet hold a spectrum of hidden networks, often referred to as the hidden web. To access these restricted spaces, one must utilize dedicated tools and techniques. Onion links serve as the gateway to these hidden realms, allowing users to navigate through anonymous and encrypted channels. These links, composed of a series of .onion domain names, route traffic through multiple layers of encryption, effectively masking the user's identity and location.
Understanding how to interact with onion links is essential for venturing into these hidden networks. Services accessible through onion links often provide anonymous communication channels, access to prohibited information, and platforms for individuals seeking anonymity.
- Concurrently, it's crucial to approach onion links with vigilance. These networks can harbor illegal activities, and users must take measures to protect their systems.
- Additionally, it's important to remember that accessing certain onion links may be against the law in some jurisdictions. Users should conduct research with relevant laws and regulations before engaging with onion links.
Diving into the Shadows: Onion Links Unveiled
The hidden web is a realm shrouded in anonymity, accessible only through specialized software. Leading users to this enigmatic world are tor links, encrypted pathways that conceal your identity and position from prying eyes. These unique URLs, often appearing as strings of incomprehensible characters, grant access to a vast network of websites that operate outside the reach of traditional search engines.
- Each onion link is generated by a complex process that encrypts your traffic, bouncing it through multiple nodes around the globe. This makes it extremely difficult to track your online activities.
- Furthermore, onion links provide a barrier of confidentiality, allowing users to surf the web without revealing their true identities.
- Nevertheless, it's important to note that the dark web is not without its risks. While it can be a useful resource for whistleblowers, journalists, and activists seeking protection, it also hosts illicit activities, such as cybercrime operations.
Venturing Through the Labyrinth: Onion Link Security Tips
In the ever-evolving digital landscape, safeguarding your online presence has become paramount. Hidden networks, also known as Tor connections, offer a layer of anonymity and security, but it's crucial to navigate them with caution. To ensure your safety while utilizing these enigmatic pathways, consider the following tips:
- Employ strong and unique passwords for each account accessed through Tor.
- Remain vigilant of suspicious pages. Verify their legitimacy before transmitting any sensitive information.
- Update your software and operating system current to patch potential vulnerabilities.
- Steer clear from openinglinks or attachments from untrusted sources.
- Implement good digital hygiene by regularly clearing your browsing history and cookies.
By observing these security practices, you can mitigate risks and utilize the benefits of Onion links in a safe and secure manner.
Onion Links: Gateway to Anonymity and Beyond
Venturing into the abyss of the internet often involves seeking a veil of anonymity. For those seeking such privacy, Onion Links present themselves as a potential gateway. These encrypted routes lead to hidden services known as .onion sites, shrouded in layers of security that make them remarkably difficult to trace.
Despite this, the world behind Onion Links is a double-edged one. It offers both safety from online surveillance and opportunity to illicit activities. The ethical implications of navigating this digital landscape are often debated.
- Individuals can employ Onion Links for legitimate purposes such as protecting their privacy during important online interactions.
- Furthermore, journalists and activists may leverage Onion Links to communicate information in regions where freedom of speech is suppressed.
- However, the anonymity offered by Onion Links can also be exploited for malicious activities such as the distribution of illegal goods or services.
Ultimately, Onion Links remain a potent tool with both beneficial and harmful implications. Their role in the evolving digital landscape is onionlinks one that requires critical consideration.
Decoding the .onion: Your Introduction to Onion Links
Venturing into the depths of the internet can be a daunting experience. Deep within this digital realm lie hidden networks, shrouded in secrecy and anonymity. These are known as shadow networks, accessible through special software and unique URLs. And at the heart of these enigmatic networks lie the hidden web addresses - a gateway to a world often untouched.
These secretive domains end in ".onion" and point to sites that operate on the Tor network. This decentralized system scrambles your connection, making it a haven for those seeking privacy or operating in restricted environments.
- Consider accessing information that's otherwise banned to the public.
- Participate in online communities where anonymity is paramount.
- Unearth a world of alternative media and perspectives.
However, remember that the dark side of this unseen web can also harbor threat. It's essential to proceed with vigilance, use strong security measures, and be aware of the likely consequences of your actions.
 Kel Mitchell Then & Now!
Kel Mitchell Then & Now! Charlie Korsmo Then & Now!
Charlie Korsmo Then & Now! Kane Then & Now!
Kane Then & Now!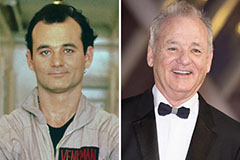 Bill Murray Then & Now!
Bill Murray Then & Now!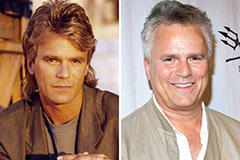 Richard Dean Anderson Then & Now!
Richard Dean Anderson Then & Now!